Introducing Inquisitorial by Indianaut, a long-form newsletter where we explain and analyze important stories stemming out of the Indian entrepreneurial ecosystem & economy.
On 28 April 2022, the Indian Computer Emergency Response Team (CERT-In) issued new guidelines for regulating information security practices, procedures, prevention, response, and reporting of cyber incidents by service providers, intermediaries, data-centers, and corporations, etc.
The new guidelines impose a larger, more complex set of obligations concerning reporting cyber incidents, storage of logs, maintaining customer information, etc., which come into effect after 28.06.2022 i.e., 60 days of such guidelines being issued.
What’s New?
For starters, all service providers, intermediaries, data-centers, corporations, and even the government bodies are required to ensure that their ICT system clocks are in sync with the servers of the Network Time Protocol (NTP) Server or National Physical Laboratory (NPL) servers of the government.
All regulated entities are mandated to report cyber incidents to CERT-In within 6 hours of noticing such incidents or being brought to notice about such incidents. Under these new guidelines, there are 20 mandatorily-reportable cyber security incidents including critical cyber incidents such as data leaks, data breaches, Compromise of critical systems/information, Unauthorised access of IT systems/data, and malicious code attacks such as virus/worms/spyware/ransomware, etc.
CERT-In may issue orders/directions to any regulated entity to take action or provide information for cyber incident response, protective and preventive actions related to cyber incidents and provide assistance to CERT-In, which may contribute towards cyber security mitigation actions and enhanced cyber security situational awareness.
All regulated entities are mandatorily required to maintain logs of all their ICT systems for a rolling period of 180 days, which is to be stored within India and provided to CERT-In whenever directed or ordered.
Data Centres, Virtual Private Server (VPS) providers, Cloud Service providers, and Virtual Private Network Service (VPN Service) providers must maintain customer data, including names, addresses, contact numbers, subscription periods, usage patterns for 5 years or longer as mandated by law.
Crypto exchanges and wallet providers must maintain all information obtained as part of Know Your Customer (KYC) and record all financial transactions for 5 years.
New Regulatory Burden
These new Guidelines are consistent with India’s approach of keeping the data at the center of the regulation rather than the users. CERT-In has unsurprisingly opted for a data hoarding and data-localization approach to Internet Regulation rather than the data-minimization principle followed under the GDPR. While the benefits of storing sensitive personally identifiable data from a safety standpoint remain to be seen, it is evident that storage of such data not only places an extra burden on the service providers but also makes the users more vulnerable in the case of a data breach.
CERT-In has increased the types of reportable cyber incidents from ten to twenty. Under these new Guidelines, the service providers are mandated to report both successful and unsuccessful cyberattacks, including, relatively benign cyber incidents such as unauthorized access to social media accounts, suspicious activities affecting systems/servers/networks/software/applications related to Robotics, 3D and 4D Printing, additive manufacturing, Drones and even AI and ML systems which can be effectively handled by the service provider and does not adversely affect critical infrastructure and the public at large.
CERT-In’s function of being the trusted referral agency for cyber users and providing a response to cyber incidents and predicting, preventing, and analyzing cyber incidents may get hampered if it has to sift through reports of such relatively benign cyber unsuccessful incidents instead of focussing on attacks on critical public infrastructure.
The new personal data storage Guidelines for VPN service providers are in-line with the recommendations by the Parliamentary Standing Committee on Home Affairs, which in its Report dated 10.08.2021 had recommended the Ministry of Home Affairs coordinate with the Ministry of Electronics and Information Technology to identify and permanently block VPNs. VPN service providers now have to maintain a physical presence in India and maintain customer data, rendering the anonymity and privacy use-cases of a VPN in India useless. Several VPN service providers have expressed their displeasure with the new guidelines as they are contrary to the 'no-logs' policy followed by some of the VPN service providers.
Similarly, Crypto exchanges, and wallets providers will have to complete the KYC requirements prescribed by RBI (KYC) Directions, 2016 of all the users and store financial transaction data, information relating to the identification of the relevant parties including IP addresses along with timestamps and time zones, transaction ID, the public keys (or equivalent identifiers), addresses or accounts involved (or equivalent identifiers), the nature and date of the transaction, and the amount transferred for 5 years. The government will now not only deduct TDS on cryptocurrency transactions, and tax your profits but also have access to all your transactions while remaining undecided on whether citizens are allowed to own cryptocurrencies issued by institutions other than Central Banks.
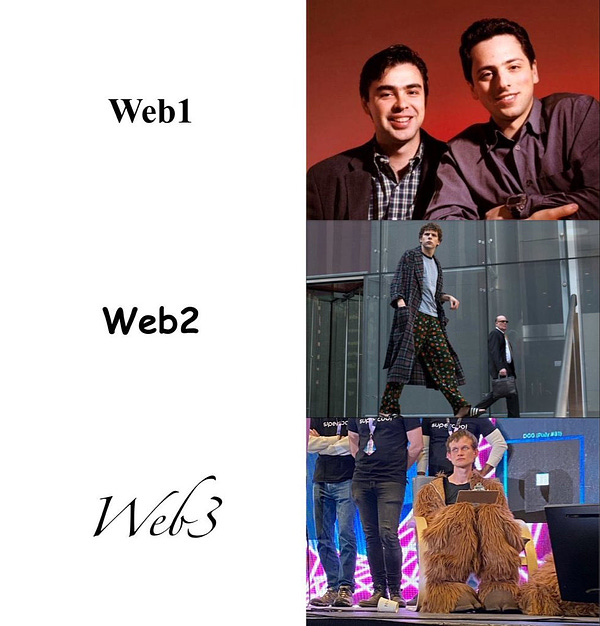
The Guidelines seem to have borrowed all the buzzwords from a web3 enthusiast’s Twitter thread but like most web3 enthusiasts, failed to provide a definitive meaning to the terms. It is unclear what falls within the ambit of “suspicious activities” which the service providers are mandatorily required to report. Whether spam emails from your favorite Nigerian Prince will be deemed to be “suspicious activity” remains to be seen.
These Guidelines are silent on the minimum security standards and encryption levels that the service providers must maintain but confine themselves to reporting protocol to be followed in response to a cyber incident.
What About the Users?
These Guidelines allow for broad user data collection and storage but are silent on the rights of the users. They do not provide for the service providers to inform the users whose data might have been affected in a cyber incident or provide any remedy for the users to secure their accounts, leaving users vulnerable to more identity theft and phishing attacks.
In absence of any data protection law or oversight mechanism on the data requests being made by CERT-In negatively impact the users as the users have no recourse against the service provider for an incident that had been reported to CERT-In or the data which has been requested by CERT-In.
Steps must be taken to ensure that cyber incidents are addressed swiftly both by the service providers and CERT-In and mechanisms are developed to provide redressal to users.